In a crisis, companies must learn to adapt as existing work processes are shut down or must be adapted to the new situation. This five-step guide helps with stabilizing business operations. In this context, the last step – the transition to normal operations – is often neglected. The right measures are required to ensure that crisis situations can be managed and that the impact on business operations can be minimized.
Identifying crises and responding promptly
What do companies have to pay attention to during a crisis?
A crisis arises, negatively affects public life and shuts down business operations. A pandemic such as the one we are experiencing at the moment is just one of a number of examples that include natural disasters, cyber attacks and other threats that can pose a grave threat to business operations and the economy. As a result, it is extremely important that companies are able to adapt as existing work processes are shut down or must be adapted to the new situation. “Adapting” is the key word for surviving during the crisis. For example, remote work, which used to be an interesting extra option, has become a necessity. This article provides an overview of what has changed, and the types of measures that can be introduced during and after a crisis.
Stabilizing business operations in five steps
What happens when your company is affected by a crisis? What is the impact of a state of emergency? These and many other thoughts have been on the minds of companies and their staff during times of crisis. Obviously, the business has to continue, even when things get very difficult. And even if a business continuity management system has not been implemented in the company to date, there are a number of simple preventative measures that can generate significant added value.
The five steps below list the possible changes that may occur as a result of a crisis, along with initial preventative measures:
Step 1: Protect employees and customers
Protecting employees and customers is the first priority – customized measures should be implemented depending on the crisis situation (pandemic, fire, flooding, earthquakes etc.). The most important objective is to evacuate employees and customers from danger zones and protect them from physical harm. Providing detailed information about the protective measures for each type of crisis would go beyond the scope of this article. Instead, we focus on the steps that are needed to stabilize business operations.
Step 2: Perform a situation and risk analysis
A suitable group of persons (a task force) should be designated after the crisis situation has been identified. The key individuals from the areas that are most critical to the business should be part of this dynamic group. The task force analyzes the present situation and the risk potential on the basis of the resources and the processes that are most at risk.
To determine the status quo, the task force should analyze the following information and questions:
- What are the most critical areas? Which departments, business processes, services and products are particularly at risk and must be maintained at all costs? What is the contingency risk?
- What areas are not as critical? Which business processes, product and services are not as critical in the current crisis and can be scaled down or even stopped in order to free up capacities, for example?
- What are the risks? What are the risks with regard to the supply chain and critical corporate resources? What risk mitigation types / measures are available in this context?
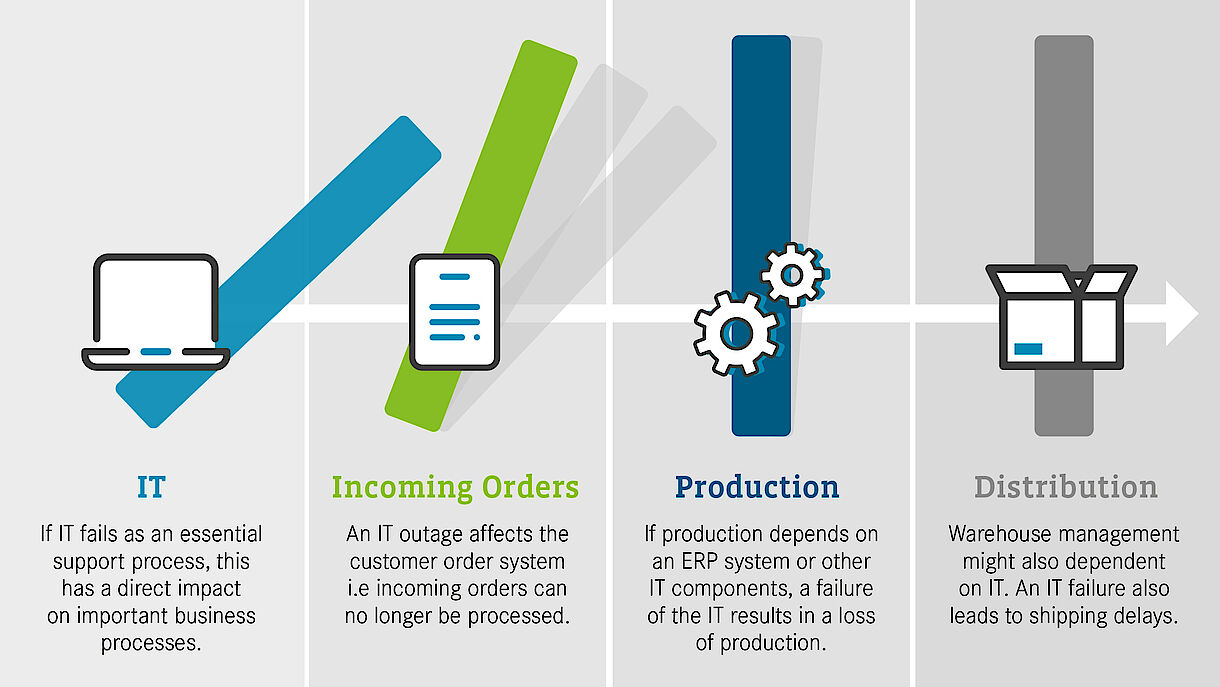
- Are there any dependencies, if any? Are there any acute dependencies between business and support processes? Which support processes must be available continuously (e.g. IT)?
- Are there enough financial resources? What financial resources have to be made available for risk mitigation purposes? What are the current financial risks? Which costs can be reduced?
Step 3: Action plan and reducing primary and secondary damages
After the current situation and risks have been identified and prioritized, realistic risk mitigation measures targeting both primary and secondary damages must also be defined.
Example of primary damages and possible risk management measures
Risk: Loss of employees due to illness (pandemic) or injury (fire, natural disasters).
Risk mitigation / risk prevention: Specific hygiene provisions, clearing of buildings and requiring people to work from home are just some examples of how imminent risks to body and life can be reduced or avoided completely as soon as possible.
Risk: Extended loss of suppliers that are relevant to critical business processes (production etc.).
Possible risk management: During a crisis, the risk analysis must be accompanied by close collaboration with your suppliers. Check with suppliers whether they have established a business continuity management system, and what their current contingency plan looks like. Early market exploration to identify potential alternative suppliers.
Risk: Loss of / severe decline in sales markets (e.g. travel/tourism industry, food service etc.) due to government orders (incoming/outgoing travel restrictions, restrictions on movement etc.) or due to an imminent recession.
Possible risk management: In the context of the crisis, the product/service and project portfolio should be re-prioritized to prepare for changing market conditions. If there is no possibility of converting operations in the short term (e.g. restaurants switching to delivery service), usually the only possibility that remains is to reduce on-going costs (reduced working hours, scaling down production, reduce services etc.) and initiate measures such as bridge financing.
Example of secondary damages and possible risk management measures
The risk mitigation/prevention of primary damages could result in new risks for secondary damages. For example, the aforementioned risk prevention strategy (clearing of buildings and requiring people to work from home) could result in the following secondary damages, which must be managed accordingly:
Risk: Capacity problems in IT due to increased remote access.
Possible risk management: The additionally required capacities should be calculated to address the higher IT capacity requirements that result from increased home office access. On this basis, companies are able to implement measures such as increasing the bandwidth for Internet access, adding more physical or virtual servers, or quickly converting to Cloud services (Microsoft Office 365, virtual desktop solutions).
Risk: Inadequate data protection / compliance for remote workplaces.
Possible risk management: The EU General Data Protection Regulation (GDPR) includes several measures that should be implemented for data protection purposes (e.g. pseudonyms or encryption). This list is not exhaustive, and what matters most is that the measures that are implemented provide a “level of protection that is commensurate to the risk”. For companies using Microsoft products (e.g. O365), Microsoft also offers configuration options and recommendations that conform to the GDPR.
Risk: Information security is negatively affected by the home office provisions.
Possible risk management: Where employees are not provided with company hardware and must use their personal computer, company data must be especially protected. There are several options for protecting company data on personal computers:
- If employees are using a personal Windows computer, the “built-in” virus protection (Microsoft Defender) in Windows can offer a minimum degree of security. It is important that this protection is not only activated but also updated regularly. Alternatively, test versions of other anti-virus companies can provide some short-term relief.
- Another option for securing data transmissions is to provide VPN/IPSEC access to the company's network. In this way, employees can establish a secure connection to their company and transfer data securely.
- Activation of multi-factor authentication (MFA) – access restriction through several passwords/attributes – for logging into your Cloud services (e.g. Office 365). This prevents access by unauthorized third parties.
Risk: Lack of targeted communication due to unaccustomed remote communication.
Possible risk management: Even if gestures and facial expressions are important components of communication, all participants have to get used to purely “speech-based meetings”. Virtual meetings often take longer and end without a result because e.g. there were problems with the transmission or interruptions due to the lack of gestures and facial expressions. Therefore it is recommended that these challenges are addressed with employees and that virtual meeting rules are established jointly.
Secondary risk: Few to no interpersonal relationships lead to decreased motivation among employees/isolation of employees.
Possible risk management: Discussions about technical issues are just as important as small talk or the social contact in the staff canteen. Therefore it is all the more important that contacts with colleagues are sought out and that needs are understood in such times of crisis. For example, “virtual coffee groups” could be a first initiative for maintaining social contacts. Encouraging employees to set up such types of meetings.
Risk: Employees are finding it difficult to work remotely.
Possible risk management: Despite the availability of new tools and the flexibility that remote working offers, you should be aware that not all employees will find it easy to work this way. Working remotely is different – being at home all day, the lack of social contact, and the disintegration of the boundary between work and free time are considered stressful by many employees. Therefore it is important to seek out conversations with employees, to reflect on the challenges and to try to find solutions. Even the simple idea of “closing the laptop no later than 6 pm” could be a possible solution. Other tips for promoting a remote work culture and virtual teams can be found in our webinar.
Risk: Managers themselves do not practice the virtual work style, which leads to lower acceptance among employees.
Possible risk management: In order to quickly respond to the needs of employees, management must also be sensitized accordingly. As in many other things, the same principle applies here as well: Acceptance among employees increases when management also accepts and practices the new way of working. Another important factor is that managers adjust their leadership style to the new digital and trust-based work situation.
The selected risk mitigation measures can be managed with a crisis management office and they can be implemented using project management methods. Additional information about project management during a crisis can be found here.
Step 4: Communications
Communication is essential during a crisis! It is used to provide key information and establishes a dialog between companies, employees and third parties. It is also a supportive measure in that it creates and promotes understanding, explains correlations and anticipates the needs and expectations of employees and third parties. Communication during a crisis says a lot about the company and should never be misused (e.g. To keep back or conceal information). Transparency is the key word for ensuring the loyalty of employees and third parties.
Communication with employees plays an especially important role during a crisis. Depending on the type and extent of the crisis, exceptional situations have far-reaching effects on people, for example if their workplaces are at risk. Despite the uncertainty, it is important that the individual concerns and fears of employees are addressed, and that solutions for the challenges are found jointly.
In the first step of employee communication, it is essential that employees are informed about the crisis situation and that instructions for conduct are provided.
A “crisis website” on the Intranet, a “black board” on the collaboration platform, crisis team meetings or information events are good examples of appropriate communication instruments during a crisis.
Step 5: Transition from crisis operations to normal operations
An exit strategy helps with gradually restoring normal operations without incurring higher risks. The lessons that can be learned from the crisis should also be part of the exit strategy. From the entrepreneurial spirit and the structure of the organization all the way to the various (key) processes, both the positive and the negative impact of the crisis should be examined. However, it is important that the analysis focuses not just on processes but also the employees (the human side). The crisis situation must be evaluated together with the employees, and the positive and negative changes, needs and insights must be documented. Measures should be developed jointly and the first initiatives should be implemented.